Security
Data security is a key part of Airflows.
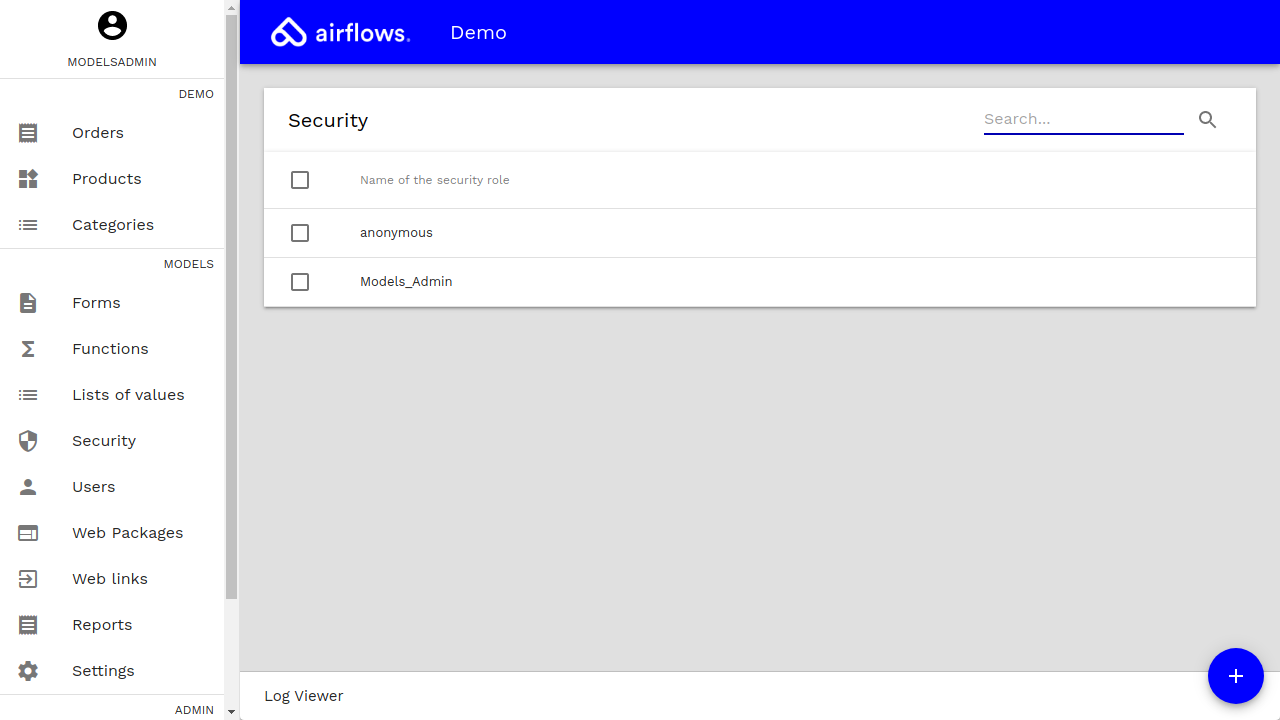
Roles
Different security roles can be defined in order for each user (i.e. Employees, Suppliers, Customers, Anonymous, ...) to have access to the allowed data only.
Roles will define several permissions.
Roles will be assigned to users in order to give them (the users) permissions to access the data.
Security can be defined at different levels (i.e. Form, Field, Row-level, Network, and Application levels).
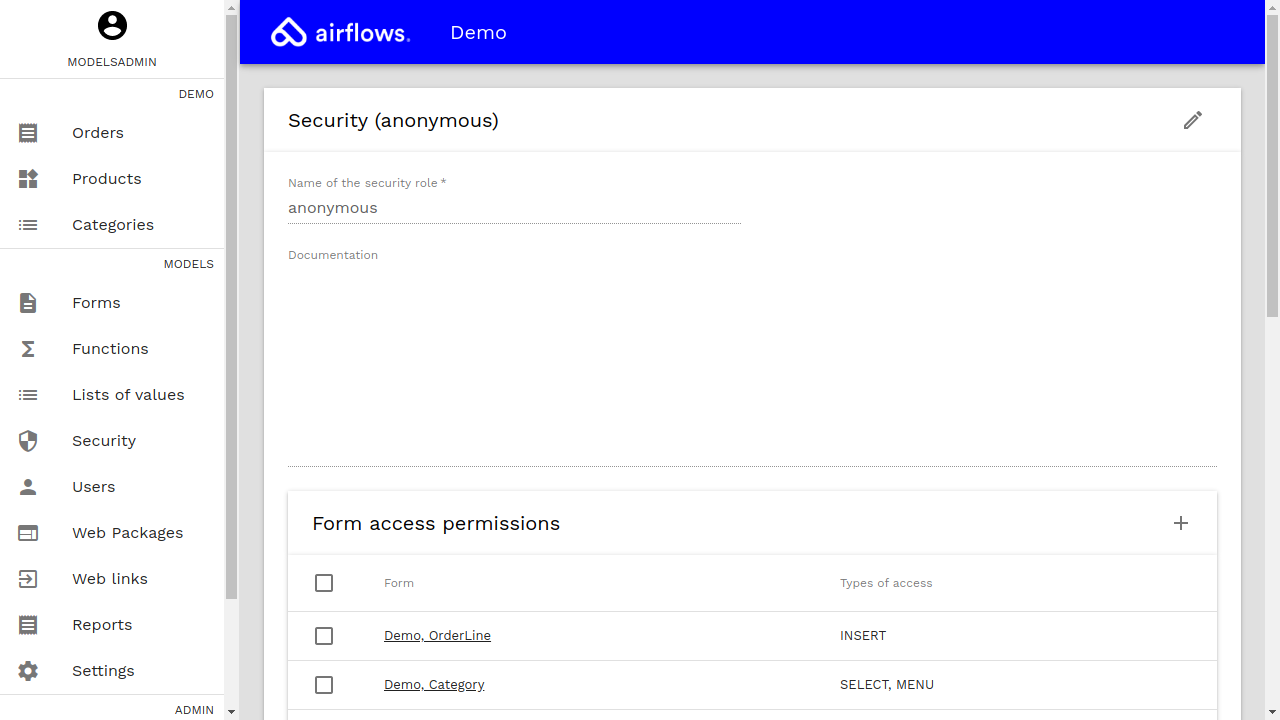
Form permissions
To define form-level permissions, the folloging parameters must be specified:
| Parameter name | Description | Example value |
|---|---|---|
| Security role | The role to which the permission applies. | Customer |
| Form | The form (entities) to which permission applies. | Demo, Product |
| Types of access | The type of accesses allowed (i.e. SELECT, INSERT, UPDATE, DELETE, MENU) | SELECT, MENU |
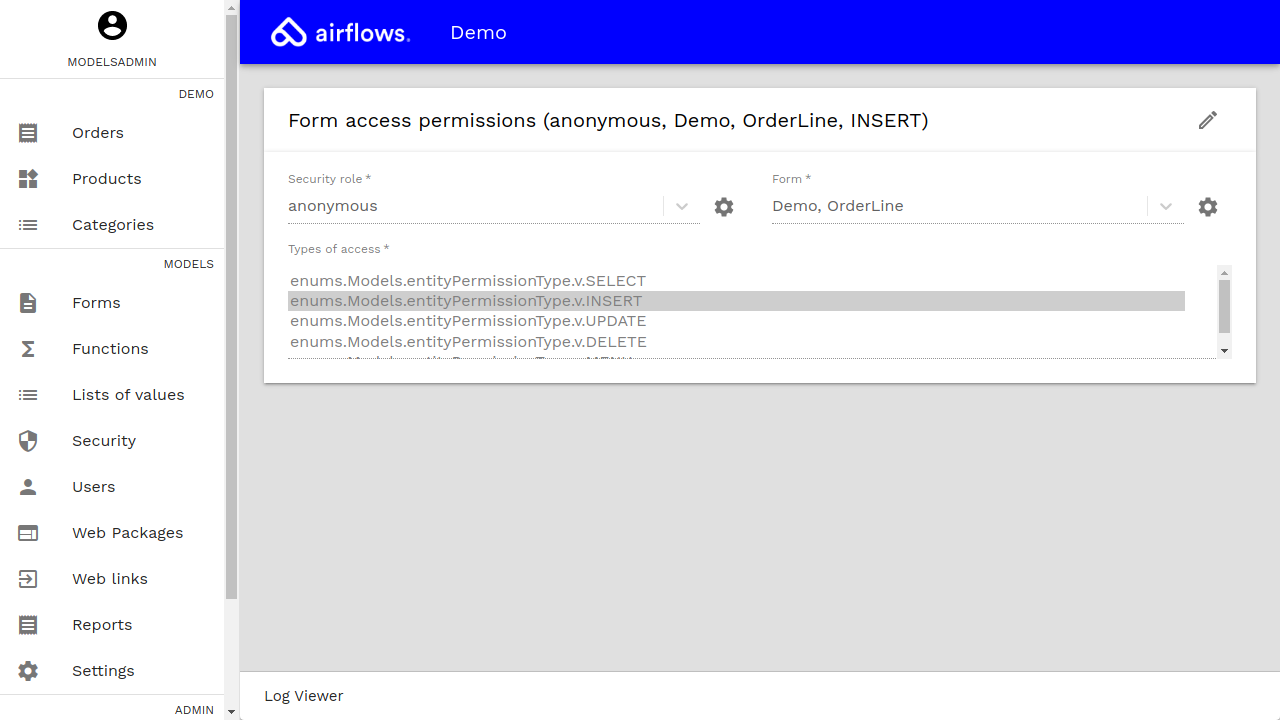
The following types are available:
| Type of access | Description |
|---|---|
| SELECT | Permission to query the data. |
| INSERT | Permission to create new entities. |
| UPDATE | Permission to update existing entities. |
| DELETE | Permission to delete existing entities. |
| MENU | Permission to access to entities directly from the admin tool menu. |
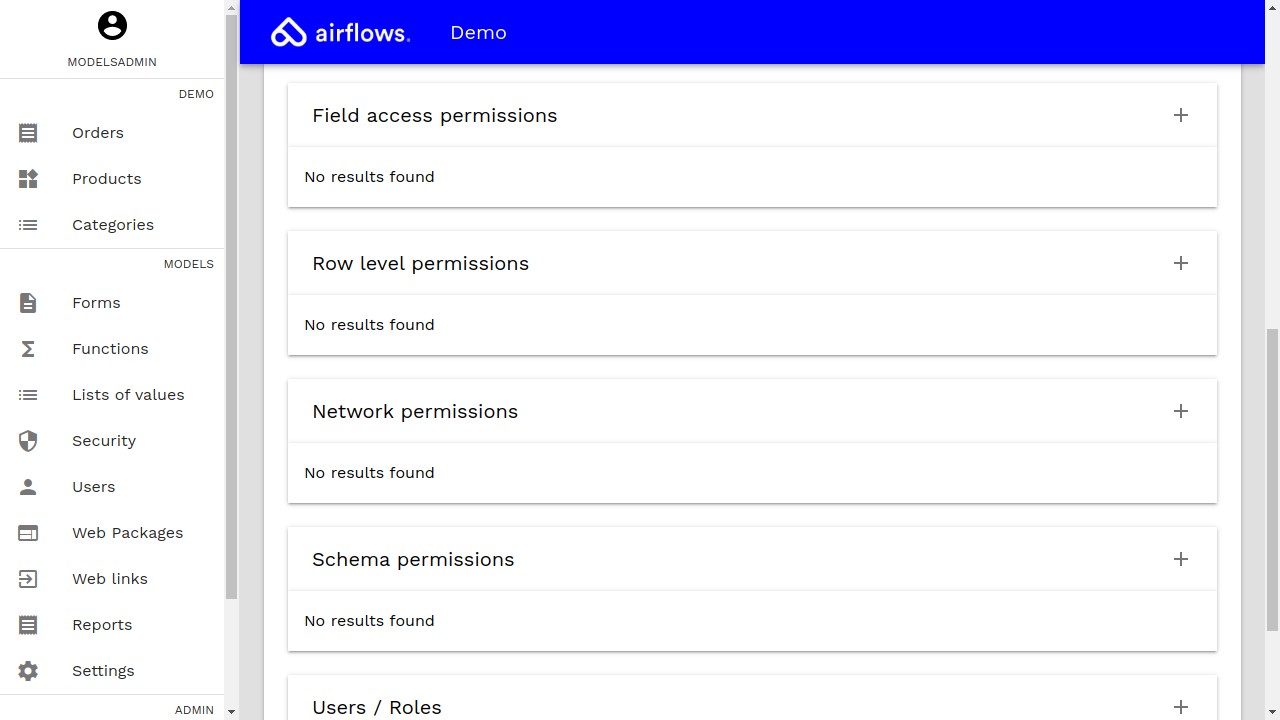
Field permissions
To define field-level permissions, the folloging parameters must be specified:
| Parameter name | Description | Example value |
|---|---|---|
| Security role | The role to which the permission applies. | Customer |
| Field | The field to which permission applies. | Demo, Product, name |
| Types of access | The type of accesses allowed. | Query permission, Permission to create |
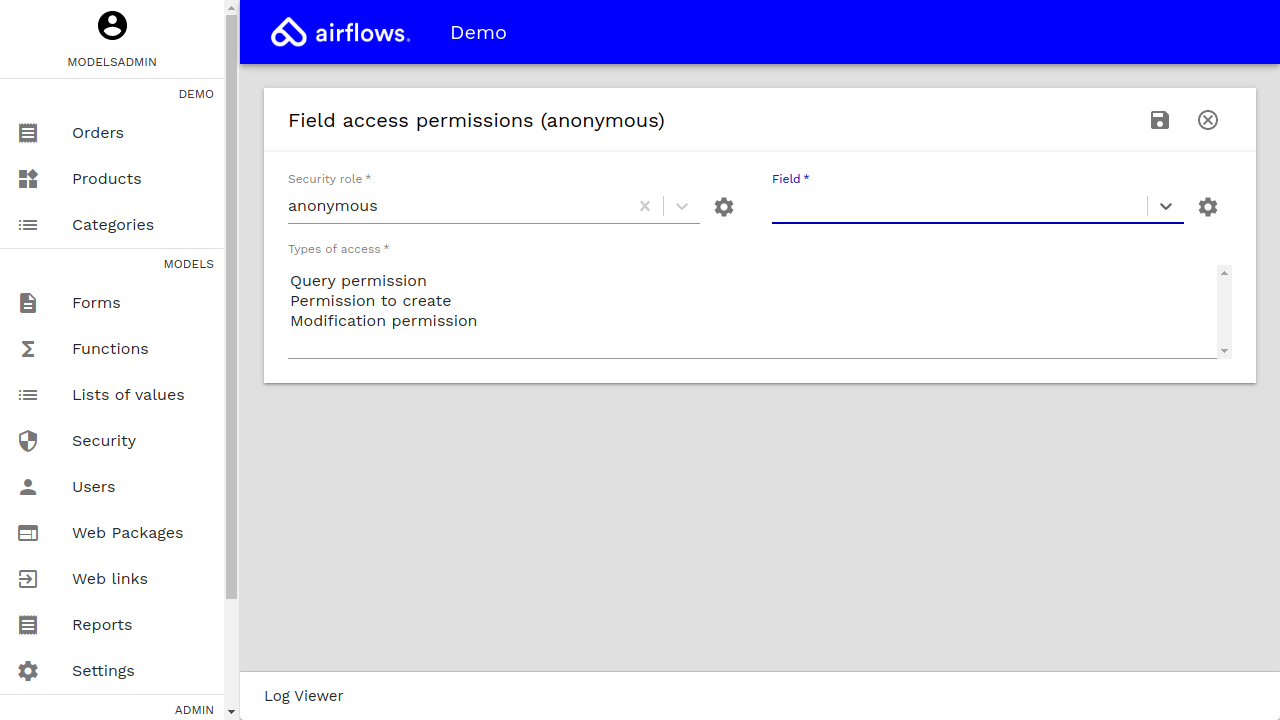
The following types are available:
| Type of access | Description |
|---|---|
| Query permission | Permission to query the field. |
| Permission to create | Permission to edit the field in new entities. |
| Modification permission | Permission to modify the field. |
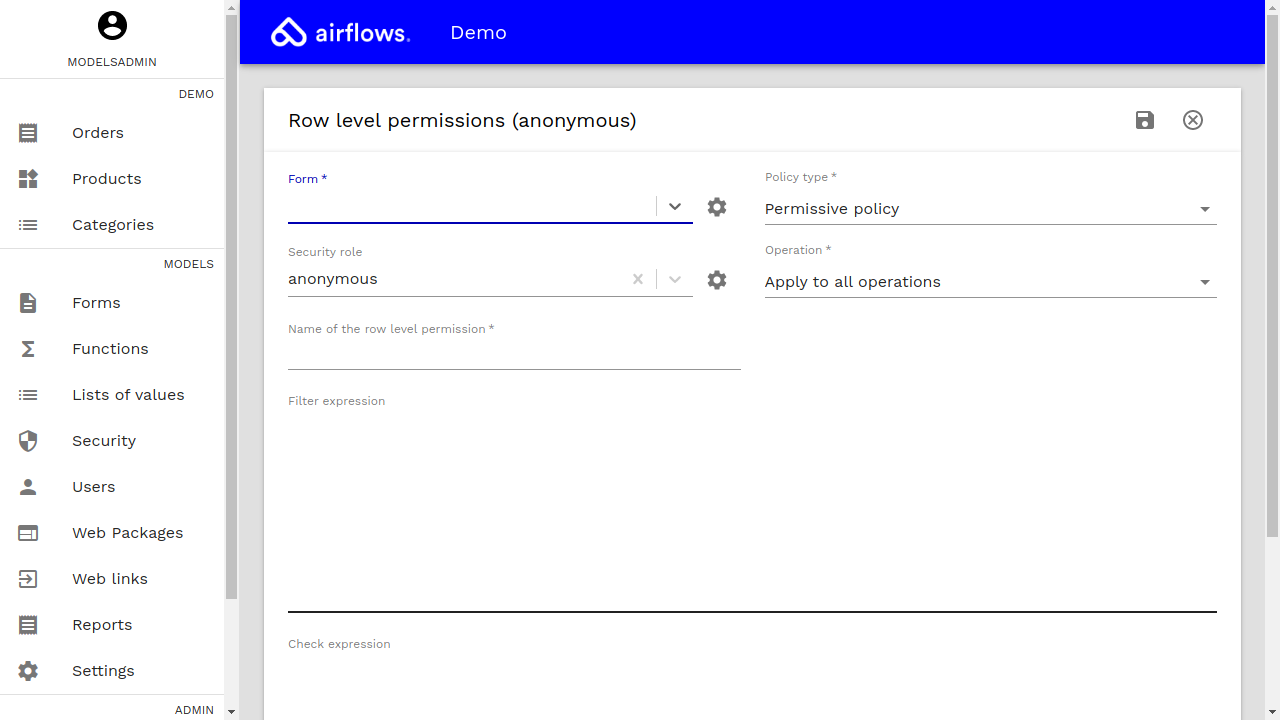
Row-level access permissions
In order to protect the data based on rules, row-level policies can be defined.
The following parameters must be defined:
| Parameter name | Description | Example value |
|---|---|---|
| Form | The form (entities) to which permission applies. | Demo, Product |
| Policy type | The type of the policy (i.e. permissive or restrictive). | Permissive |
| Security role | The role to which the permission applies. | Customer |
| Operations | The operations to which the policy is applied to (i.e. all, query, insert, update, delete). | Apply to all operations |
| Name of the permission | The name of the permission. | Published products only |
| Filter expression | Filter expression that applies to selected entities (SELECT, UPDATE, DELETE). | state = 'published' |
| Check expression | Check expression that applies to modified entities (INSERT, UPDATE) if different from filter expression. |
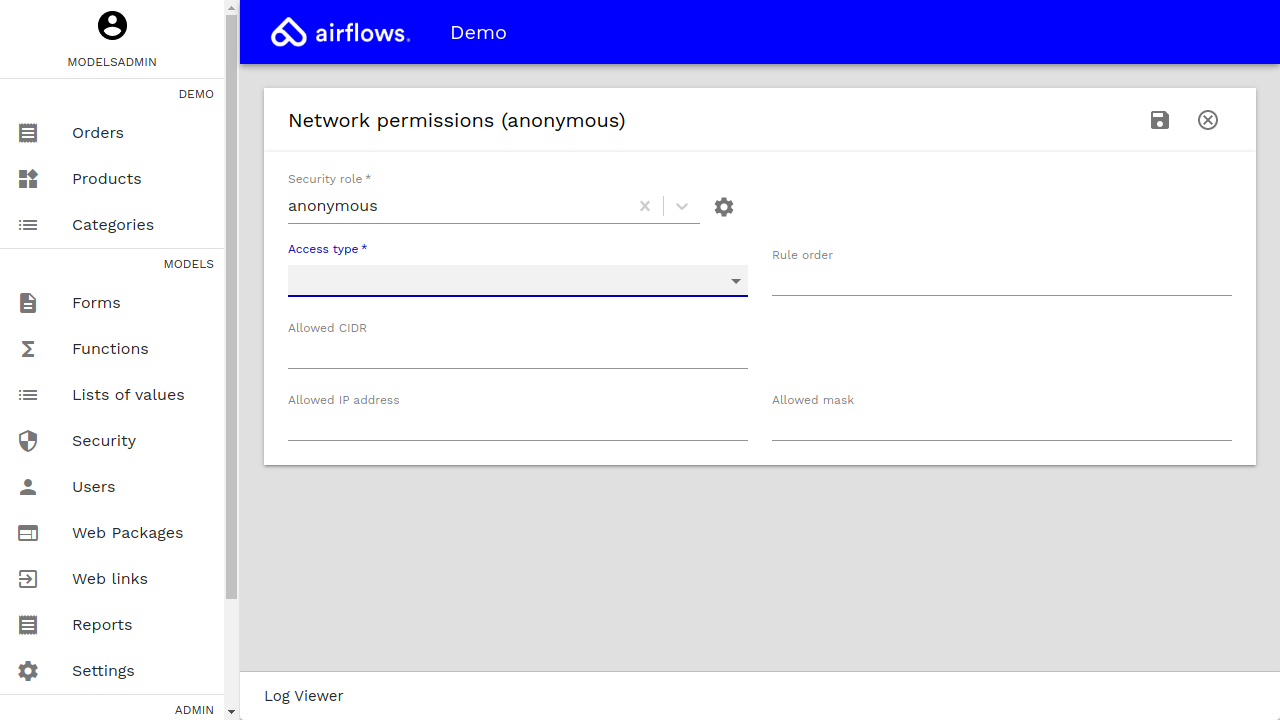
Network permissions
Access to the platform can be accepted or rejected defining different network source rules.
The following parameters can be defined:
| Parameter name | Description | Example value |
|---|---|---|
| Security role | The role to which the permission applies. | Customer |
| Form | The form (entities) to which permission applies. | Demo, Product |
| Access type | The type of the access (i.e. Accept or Reject). | Accept |
| Rule Order | Order of the rule in the iptables chain. | 1 |
| Allowed CIDR | The CIDR to which the permission applies. | 192.168.100.14/24 |
| Aloowed IP address | The IP address to which the permission applies. | 192.168.0.0 |
| Allowed mask | The address mask to which the permission applies. | 255.255.255.0 |
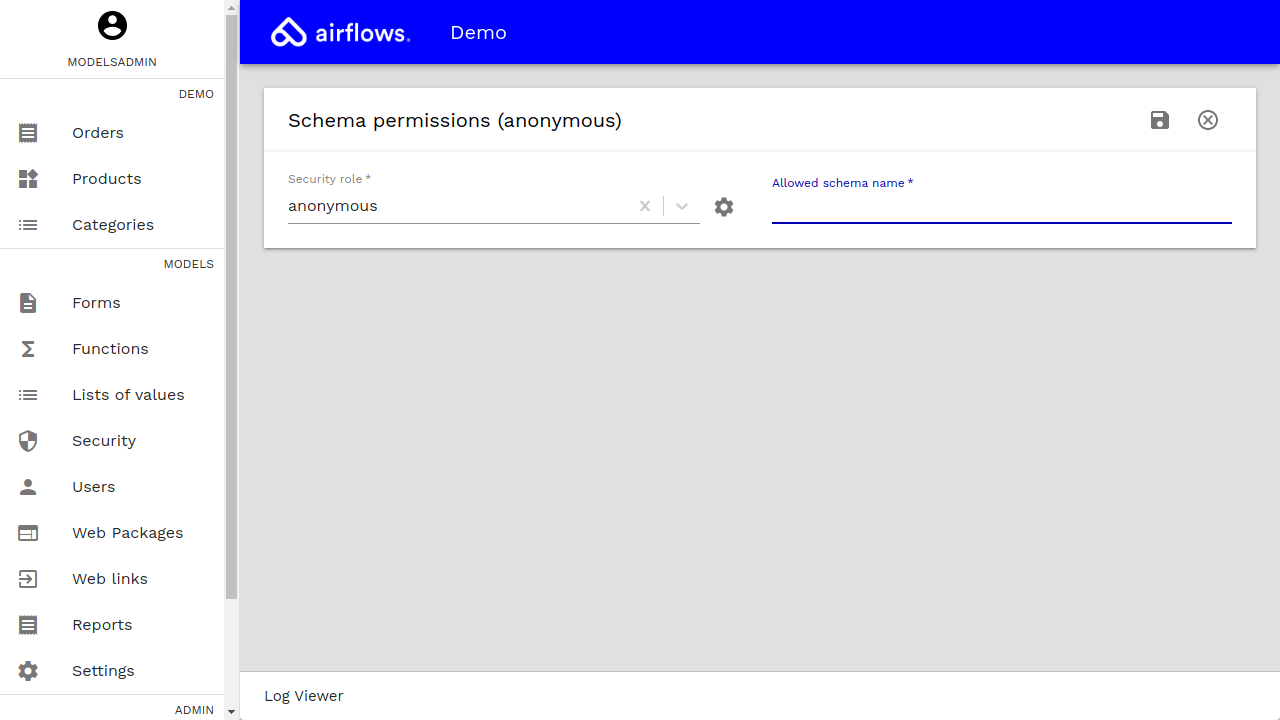
Application or schema permissions
Access to modeled applications can be allowed or restricted to different roles.
The following parameters can be defined:
| Parameter name | Description | Example value |
|---|---|---|
| Security role | The role to which the permission applies. | Customer |
| Allowed schema name | The schema or application to which permission applies. | Demo |
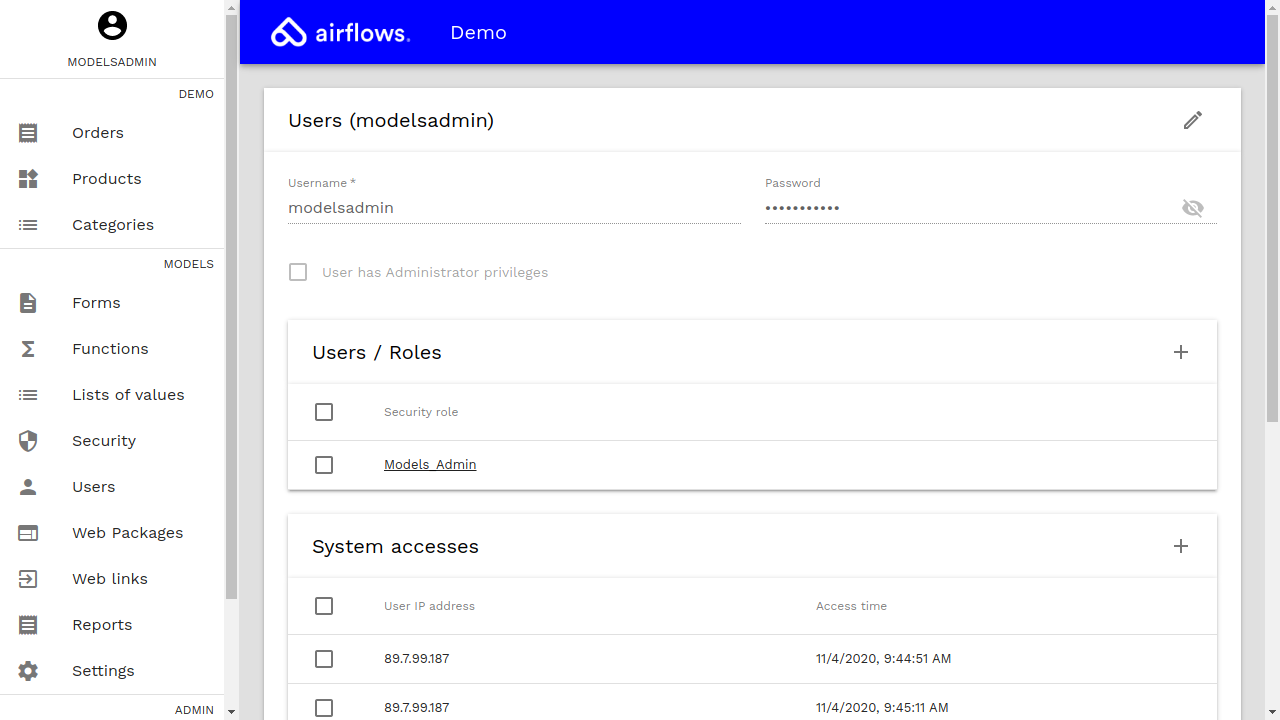
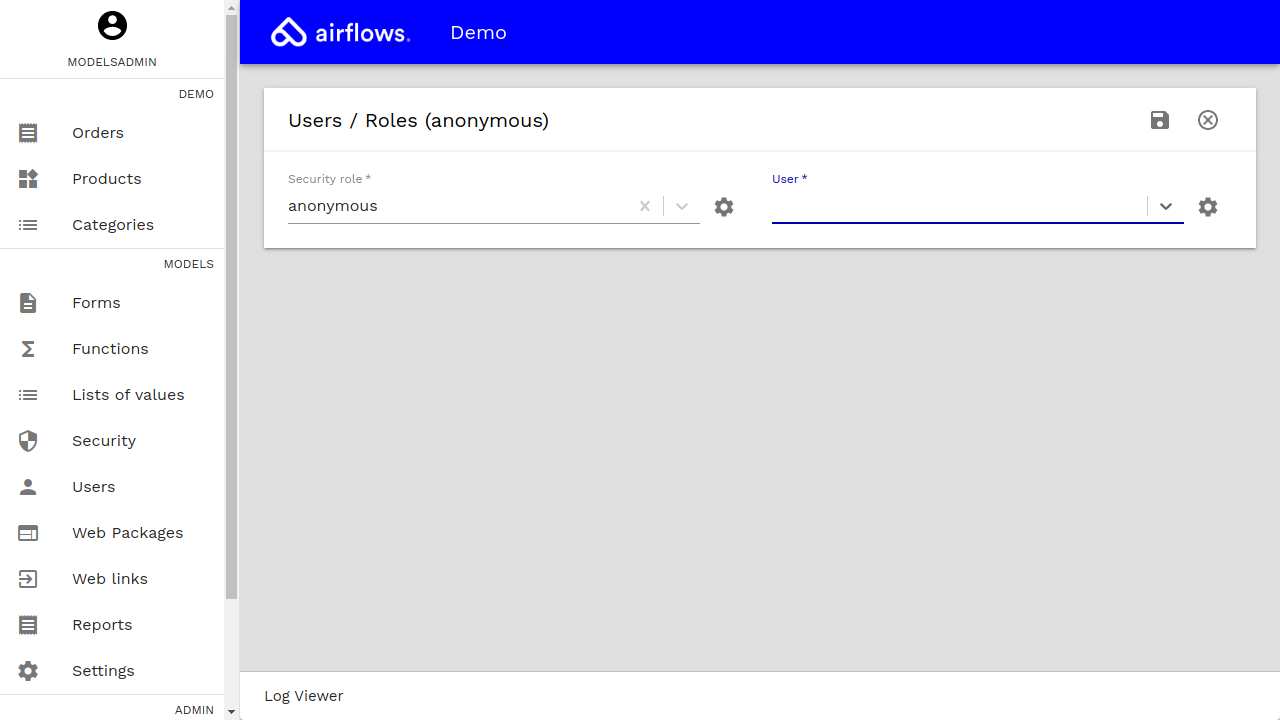
Users
Once the roles are defined, they can be assigned to users.
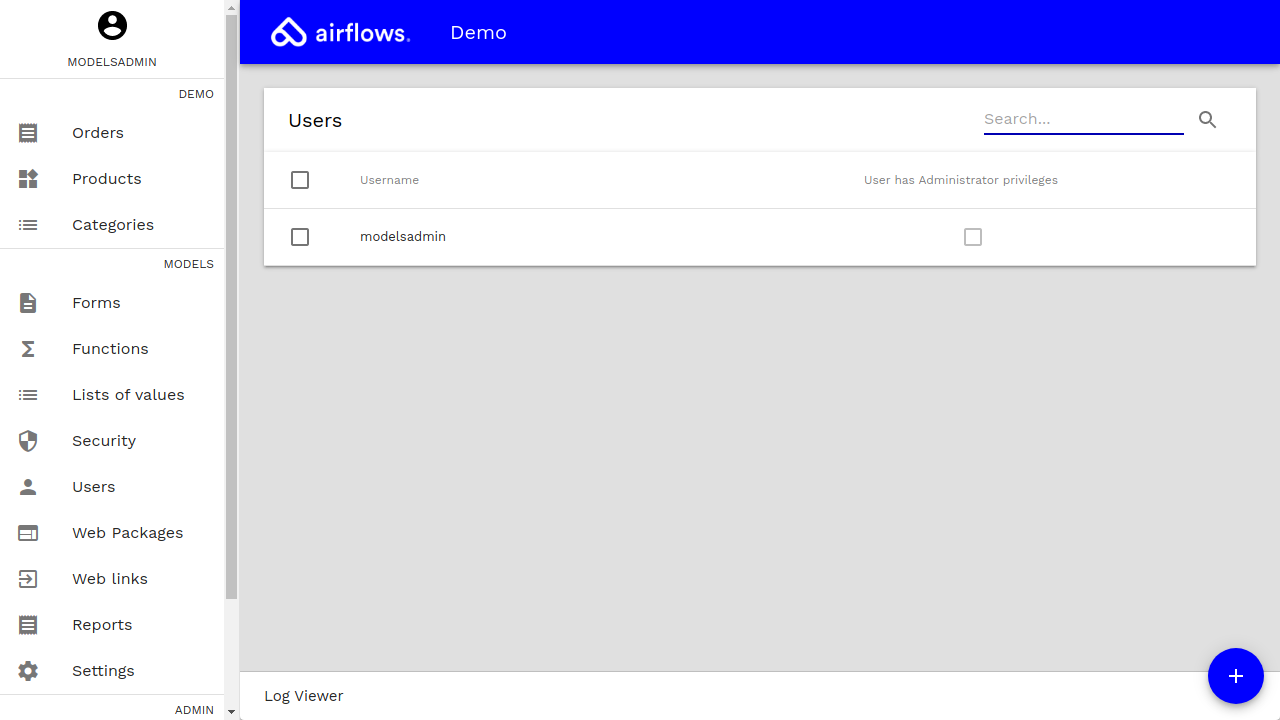
Each users can have several roles.
Users accesses to the platform are logged.